Las Vegas is a hyper-connected city. It’s also home to some significant cyber security flaws.
In 2021, the number of connected devices in the city of Las Vegas was astronomical. Out of the total number of devices, roughly 480,000 were easily discoverable and searchable through platforms like Shodan, a public search engine that anyone can access and use.
In addition to the devices that are publicly visible, there are a wealth of smart devices in the greater Las Vegas area, both in homes and business (including casinos). Considering Las Vegas’ population of approximately 650,000 and collection of around 200,000 slot machines (many of which are connected devices), it’s not unlikely that the total number of connected devices in the city reaches up to around 10 million, one million of which are present in casinos.
Las Vegas is also host to a significant number of annual conferences and events, including significant industry events such as CES in the example ahead. We ask the question, what is the impact of this number of connected devices on the cyber security of large-scale events?
Let’s begin with dissecting the purpose of the nearly half a million connected devices that call Las Vegas home and can be easily searched for. Some of these devices are honeypots (in other words, decoys that have been set up to protect network security), while others are straightforward IoT devices that play rather insignificant roles (think smart household appliances).
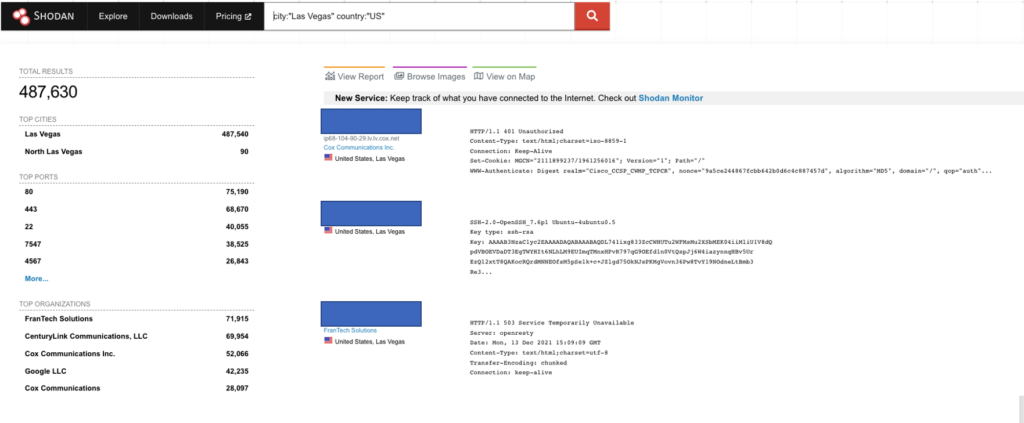
An overview of connected devices in the city of Las Vegas (via Shodan.io)
A small portion of Las Vegas’ IoT devices, however, can play a crucial role in keeping the city both safe and up and running. Read on as we analyze what an attacker can do to take on smart devices widely used throughout the city and how a large event like CES could potentially be impacted by security flaws.
Why is Las Vegas’ IoT security important?
It almost goes without saying that Las Vegas is a hyperconnected city – mainly due to all the city’s casinos implementing CCTV monitoring systems and modern gambling machines, which are all connected to a network. When this implementation is carried out correctly, it can be an amazing help in managing the casinos, surveillance systems, and city security in general. However, these systems aren’t always set up perfectly.
Here are a few examples of the use of flawed systems and their potential consequences.
Running old operating systems in casinos
A good portion of Las Vegas’ casinos make use of up-to-date operating systems in their hardware, such as Debian, Ubuntu, and others. However, there are others that are still running outdated systems like Windows Server 2008, 2012, and 2016.
The Windows Server 2008 R2 can especially be an issue, as it’s no longer supported by Microsoft. In fact, there are a total of 2,091 known vulnerabilities that can be used to target this particular operating system. Many of these vulnerabilities can be exploited to grant hackers wider device privileges — this, in turn, can be used to circumvent user authentication.
So, what does this mean in practice? For starters, it’s easy for almost anybody to find the device running outdated operating systems, research the appropriate attack vector online and execute the attack.
It’s worth noting that on the server, I was able to locate several email servers and local databases collecting casinos’ daily data. It’s not a wise idea to have any of this information leaked outside the company.
Using vulnerable IoT cameras
In the Shodan data presented above, there are a whopping 2,823 Hikvision cameras that are easily visible. This makes them the most widespread device of all the visible connected gadgets in Las Vegas. The problem is that these particular cameras were recently targeted with Moobot botnet, which also currently makes them one of the most popular targets.
In cameras that have fallen victim to this attack, cybercriminals can run privilege escalation and enslave the camera to do virtually anything that they want. An updated patch was already released by Hikvision in September 2021; however, it appears that roughly 90% of the cameras in Las Vegas have not yet been updated to the latest, secure firmware.
NAS devices are everywhere
Network Attached Storage (NAS) devices are primarily used as a central location for authorized users to store and access data. It can sometimes happen that the security of NAS devices becomes compromised, and when that occurs, the risks are big. In short, NAS vulnerabilities can allow for full takeover of devices from the network, including access to a user’s stored data, without any prior knowledge. Earlier this year, NAS manufacturer Synology revealed remote code execution vulnerabilities present in some of their devices.
In practice, NAS devices are put to use in many networks for an array of different use cases. In a city like Las Vegas, NAS devices could serve as CCTV storage, which would potentially involve the storage of online data from the guests of hotels and casinos. This being the case, having vulnerable NAS devices in a network can put an entire organization at risk.
While we don’t believe that these vulnerabilities would significantly disrupt an event like CES, it’s important to keep the inner workings (and potential weak spots) of hyperconnected networks in mind.
—————————————-
For more information relating to nothing in the article, please feel free to get in touch with us here at SAM.




